Layer 8 Technology: How We Protect Users at our Plattsburgh Office
4.7 (183) · $ 14.00 · In stock
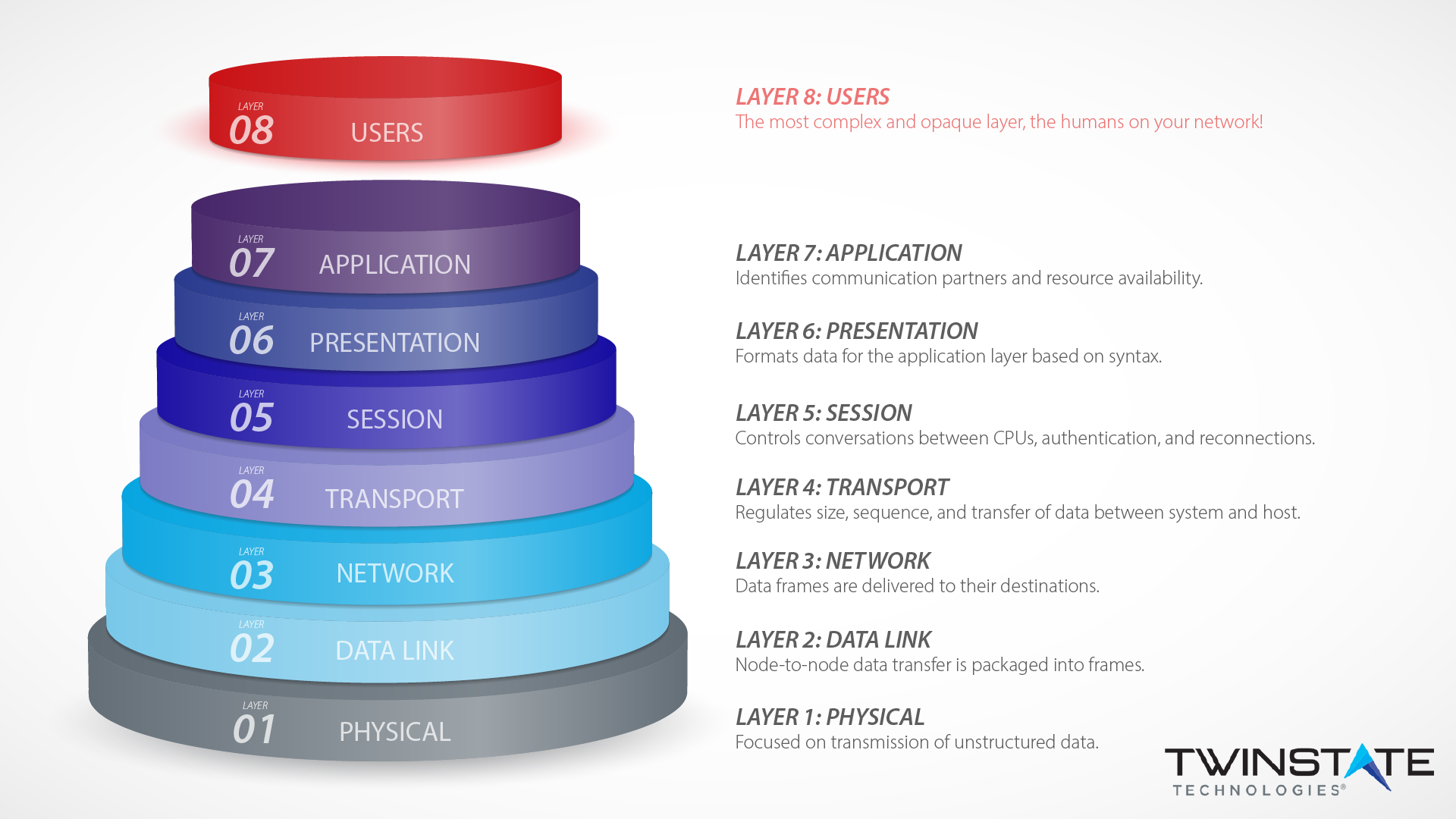
Layer eight security depends on end-users according to the OSI model. Learn how Twinstate Technologies protects the users at our Plattsburgh, NY office.

Instant Download Ebook PDF Basic Statistics For Business and
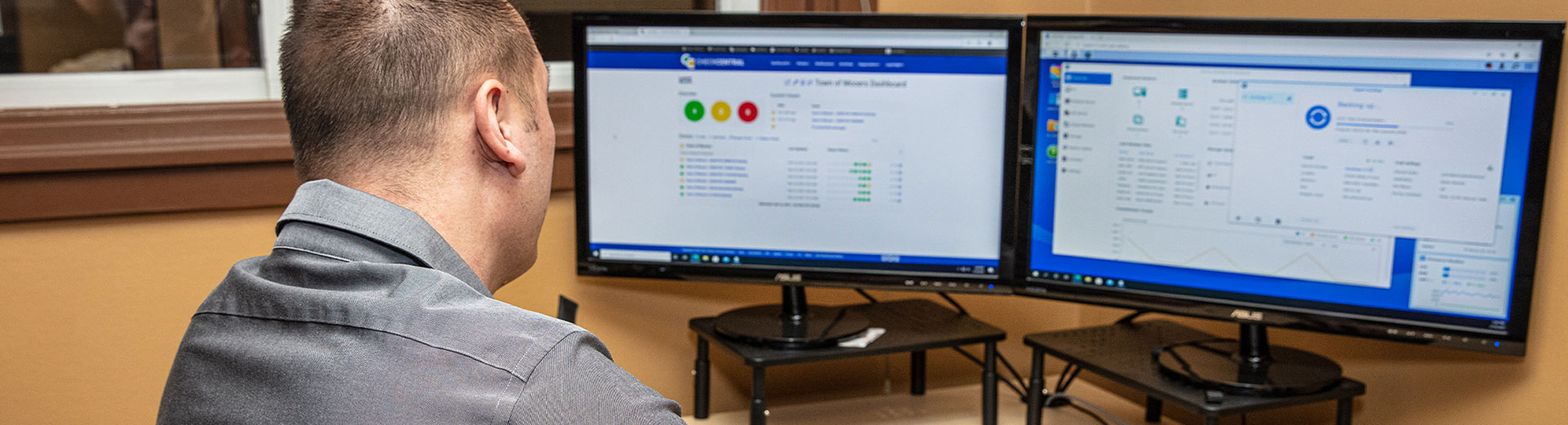
All-Inclusive, Fully Outsourced IT Management

Spill of landfill leachate into stormwater pond leaves Coventry
Securing Layer 8 – Open Sourcerers

Online Cisco CCNP Enterprise: ENCOR & ENARSI from Champlain Valley
What is 'Fly By Wire' technology? Do all modern combat aircraft

KPMG University Connection

G & G Tire Company Inc., Tires & Automotive Repair

Patient Portal - Hudson Headwaters Health Network
PPT - A Method for Projecting Individual Large Claims PowerPoint

Ease Your Anxious Attachment Style With These Affirmations

From Day One September Virtual: New Ideas for Successful