Tighten SSH access to your cloud resources using short-lived SSH certificates
4.8 (444) · $ 18.00 · In stock
SSH access using public private key based authentication has several drawbacks that could potentially compromise your organization’s SSH access security. SSH certificate based authentication is a great alternative that addresses most of these security problems.
SSH Certificate Rotation
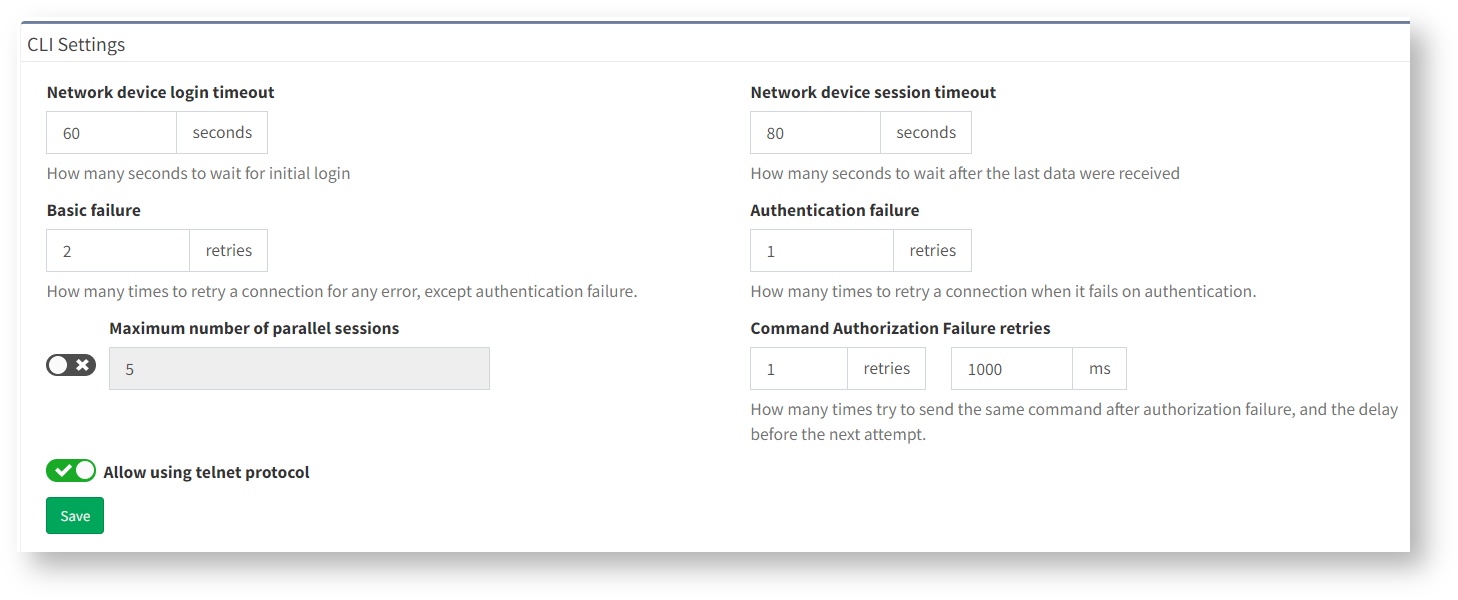
SSH/TELNET - IP Fabric Documentation Portal

Using AWS Client VPN to securely connect to RDS

Short-Lived Certificate in Browser SSH doesn't work at all
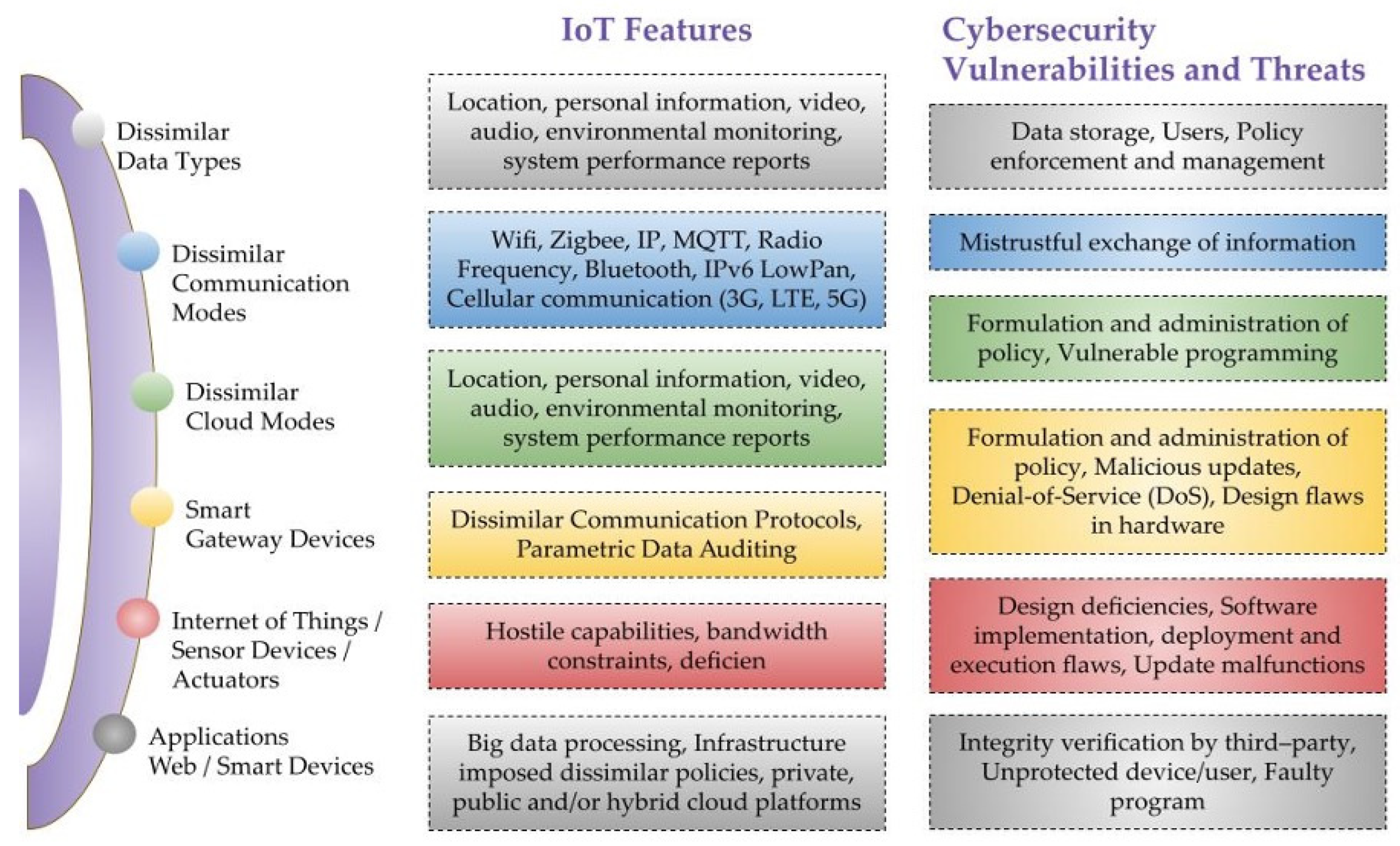
Sensors, Free Full-Text

How to configure and setup SSH certificates for SSH authentication

How do I use SSH to connect to a remote server in Linux
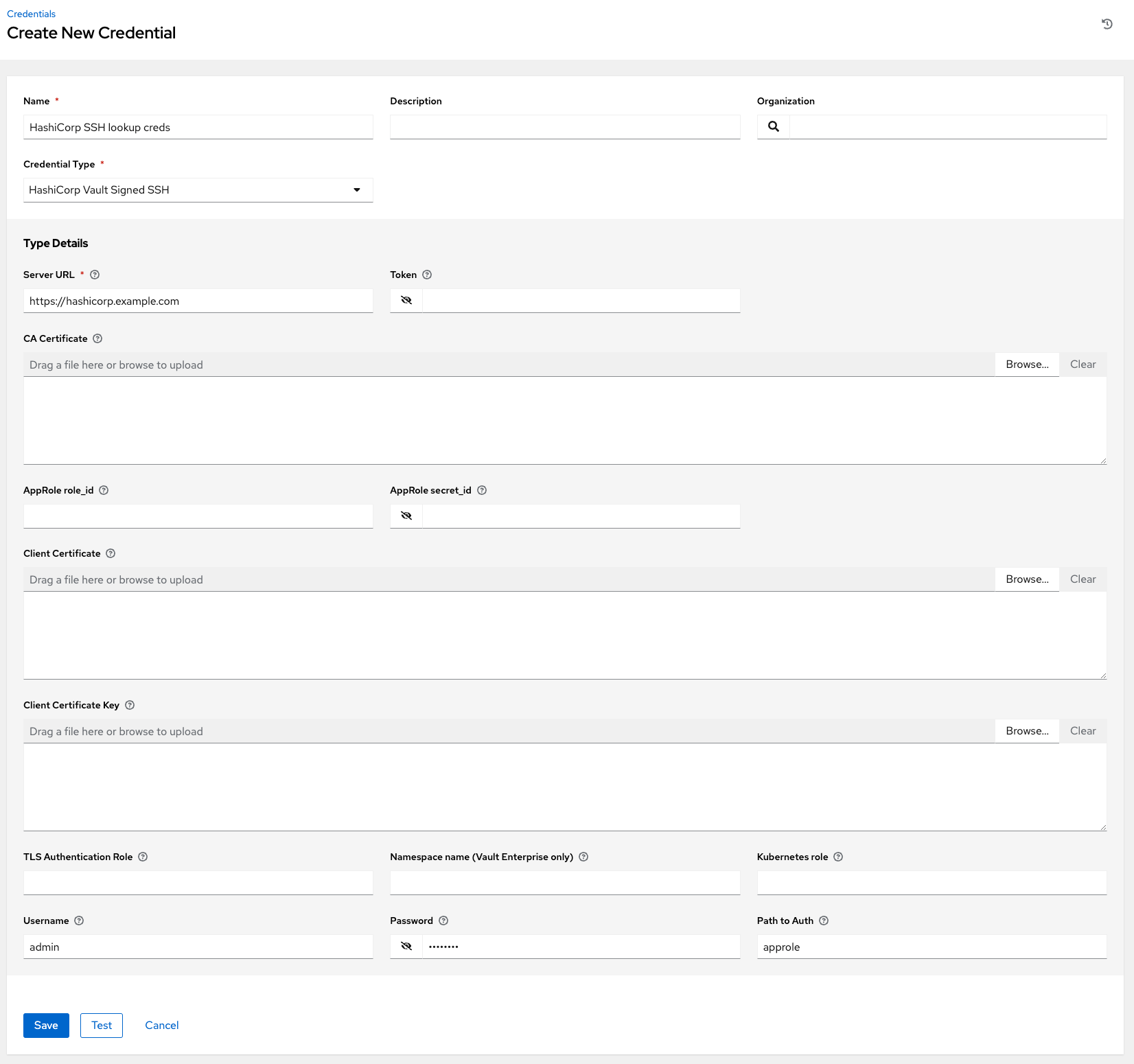
Automation Controller User Guide Red Hat Ansible Automation

SSH Key Management Overview & 10 Best Practices

SSH Certificates: A way to scale SSH access – Rootconf 2019
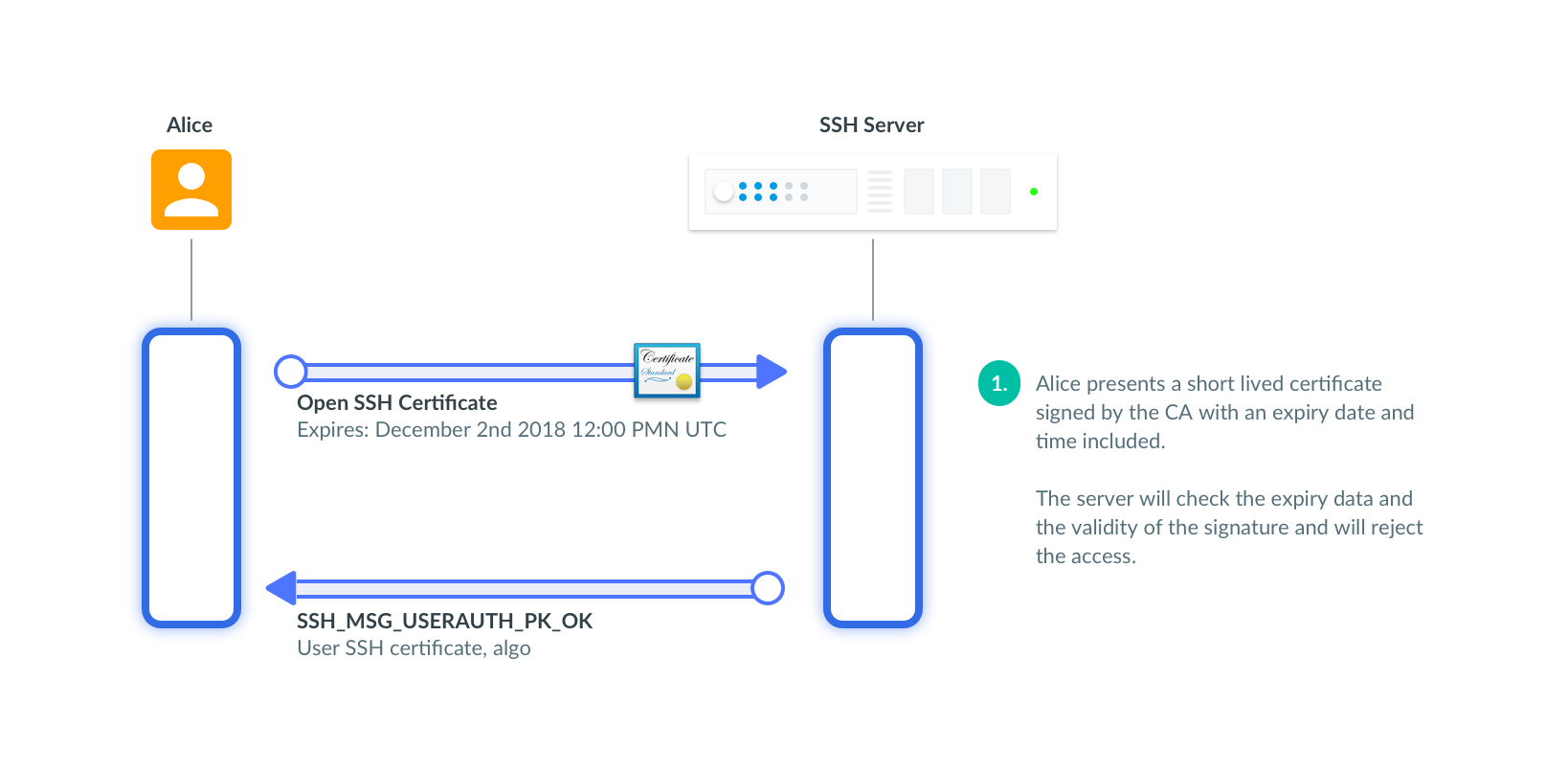
SSH Certificates Security Hardening
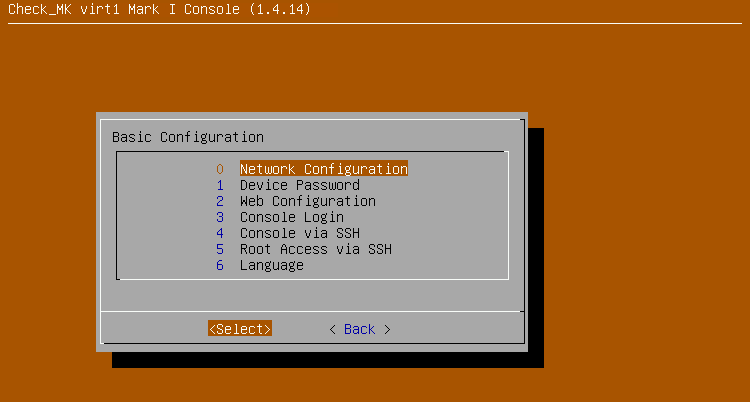
Configuring and using the appliance
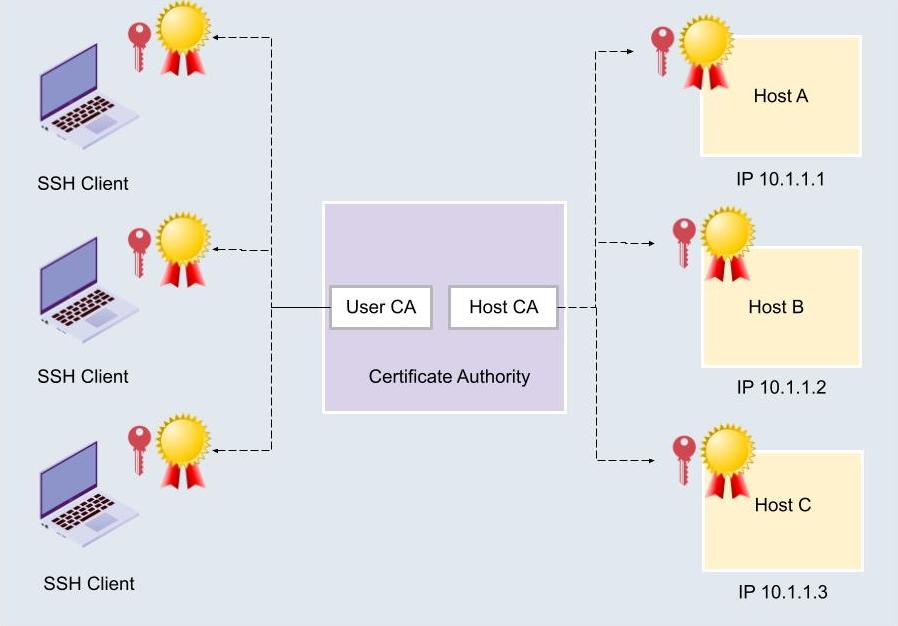
How to configure and setup SSH certificates for SSH authentication




)






